Getting authentic insights from research depends entirely on the quality of your data. But with remote studies, how can you be sure the person on the other end is real, unique, and qualified? It’s a serious challenge, especially when you consider that roughly 20% of market research responses might involve bogus data. In some industries, fraudulent responses can be as high as 26%.
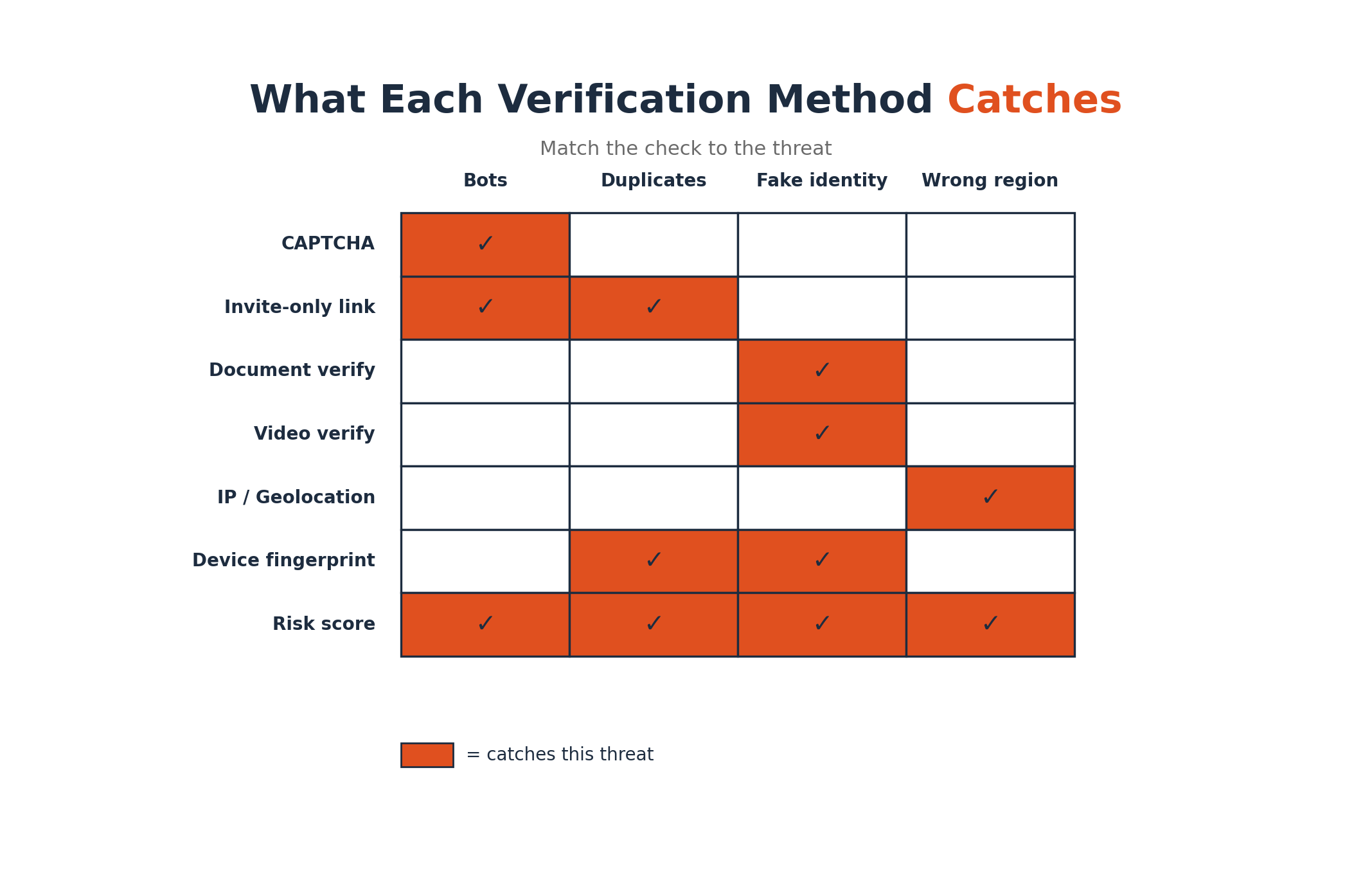
When your decisions rely on that data, you can’t afford to get it wrong. The solution for how to verify participant identity in remote studies is a layered approach, combining automated checks, direct identity confirmation, and background technical analysis. This guide offers a comprehensive look at these methods. From simple bot filters to sophisticated video checks, we’ll cover the tools you need to protect your research, ensure data integrity, and gather insights you can trust.
The First Line of Defense: Simple and Automated Checks
Before you even get to verifying specific details, you can put powerful, automated barriers in place. These initial steps filter out low effort fraud and streamline your process.
CAPTCHA and Bot Filters
You’ve seen them everywhere: the distorted text, the “select all images with a bus” grid. A CAPTCHA (Completely Automated Public Turing test to tell Computers and Humans Apart) is a simple test to distinguish people from automated bots. With automated bot traffic now surpassing human traffic online, a CAPTCHA is a crucial first step. It acts as a bouncer for your survey, preventing scripts from flooding your study with fake responses.
Invitation Only Survey Links
An open link posted on the internet is an invitation for trouble. A much more secure method is using invitation only links. Each pre screened participant receives a unique URL that expires after one use. This simple strategy achieves two key goals:
Using Survey Platform Security Features
Most modern research platforms have built in tools to help with security. Before launching any study, it’s worth exploring your platform’s settings. Look for features like:
Platforms purpose built for secure research, like Yazi, integrate these protections by default (see Yazi’s Data Security Executive Summary). For example, by running studies on WhatsApp, it leverages an ecosystem where users are already tied to a verified phone number, adding a layer of authenticity from the start.

Verifying Who They Are: Direct Identity Checks
When you need a higher level of certainty, direct identity verification methods are the way to go. These techniques confirm that a participant is exactly who they claim to be.
Consent and Privacy Notice for ID Checks
Before you ask for any personal ID, you must get explicit consent. A clear consent and privacy notice explains why you need to verify their identity (to prevent fraud), how their data will be used, and how it will be protected. This is not just good practice, it’s a legal requirement under regulations like GDPR and POPIA. Being transparent builds trust and makes participants more comfortable with the process. See Yazi’s Privacy Policy for how participant data is handled.
Document Verification
Document verification involves asking a participant to submit a photo or scan of a government issued ID, like a driver’s license or passport. Some studies might ask for a utility bill to confirm an address. While this adds a step for the participant, it is a powerful deterrent for fraudsters. Many legitimate panel providers perform an ID check during sign up as a standard quality control measure.
Video Verification
Video verification takes this a step further by asking the participant to appear on a live or recorded video, often holding their ID next to their face. This confirms “liveness” and makes it extremely difficult for someone to use a stolen or fake identity. An agent or an AI system (such as Yazi’s AI Interviewer) can then verify that the face on the video matches the photo on the ID. The process brings a face to face level of trust into the digital world, which is a key part of how to verify participant identity in remote studies.
Live Confirmation Call
A quick phone or video call can work wonders. A researcher can call a participant to ask a few follow up questions about their screening answers. Their ability to speak confidently and knowledgeably about a topic is often a clear indicator of their authenticity. Some research firms even ask participants to send a selfie with a product they claim to own, which is then verified during the call.
Mailing Address Verification
Confirming a participant’s physical mailing address adds a real world anchor to their digital profile. This can be done by checking the address against postal databases. Some panels even mail a postcard with a unique verification code that the participant must enter online, proving they have access to that physical address. This makes creating multiple fake accounts much more difficult.
Verifying What They Know: Competence Checks
Sometimes, it’s less about who they are and more about what they know. For specialized B2B or healthcare studies, ensuring participants have the right expertise is critical.
Credential Verification
Credential verification confirms a participant’s professional qualifications. Instead of just taking their word for it, researchers can take extra steps to validate their claims. This might involve:
Pre Screen Knowledge Check
A pre screen knowledge check, sometimes called a “red herring” question, is designed to catch inattentive or dishonest respondents. It can be a simple instruction hidden in a question (e.g., “Select the number 3 below to continue”) or a basic knowledge question that a true professional would know instantly. This simple technique is highly effective at filtering out people who are just clicking through to get an incentive. For inspiration, browse this survey question bank for attention‑check and knowledge‑check ideas.
Digital Sleuthing: Behind the Scenes Technical Checks
Some of the most powerful methods for how to verify participant identity in remote studies happen entirely in the background, analyzing digital signals to spot fraud.
Device Fingerprinting
Device fingerprinting creates a unique identifier for a participant’s computer or smartphone based on its specific configuration (OS, browser, screen resolution, fonts). This “fingerprint” is more stable than an IP address and is incredibly effective at catching a single person trying to complete a survey multiple times from the same device, even if they use different names or a VPN.
IP and Geolocation Check
Every device on the internet has an IP address, which can be traced to a general geographic location. An IP and geolocation check helps ensure your participants are coming from the correct country or region. If you’re running a study for people in Kenya, an IP address from Eastern Europe is an immediate red flag. This also helps detect if many responses are coming from the very same IP address, suggesting a single person is “ballot stuffing.”
Session Geofencing
Session geofencing takes this a step further by creating a virtual boundary for your study. It restricts access in real time, so only people physically within the approved geographic area can participate. This can be done using IP addresses or, for mobile studies, the device’s GPS. It’s an invisible way to ensure your location specific research is genuinely local. Learn more about How Yazi works to implement geofencing and other in‑chat controls.
Digital Footprint Check
A digital footprint check examines a person’s online presence to confirm they are a real individual. Services can check if a participant’s email or phone number is associated with various social media profiles and online platforms. A brand new email address with no online history is suspicious, while an email linked to multiple active profiles suggests a legitimate person. It’s very difficult for a fraudster to fake years of natural online behavior.
Duplicate Detection
Duplicate detection is the process of finding and removing responses from the same individual. This is done by cross referencing multiple data points, including email addresses, phone numbers, IP addresses, and device fingerprints. The goal is simple: one person, one response.
Fraud Detection Service Risk Score
You can also use specialized third party services that provide a real time fraud risk score. These services analyze hundreds of data points (IP reputation, email history, proxy use, etc.) and return a score indicating the likelihood of fraud. In one study, every survey response with a risk score above 59 turned out to be fraudulent. Researchers can set a threshold to automatically block high risk participants or flag them for review.
Maintaining Quality During and After the Study
Verification doesn’t end once the survey begins. Keeping an eye on quality throughout the research process is a crucial part of how to verify participant identity in remote studies.
“Video On” Policy in Zoom
For qualitative research like focus groups or interviews conducted on Zoom, a mandatory “video on” policy is essential. It ensures the right person is participating and that they are actively engaged. It’s easy to spot an imposter (like a teenager standing in for an adult) and helps the moderator gauge nonverbal cues and attentiveness.
Incentive Verification Before Payment
Before you send out that gift card or cash payment, a final check is in order. Incentive verification is the process of confirming a participant completed the study honestly and met all requirements before paying them. This involves checking for things like:
This final quality gate ensures your research budget is spent only on valid, high quality data.
Conclusion
There is no single magic bullet for how to verify participant identity in remote studies. The strongest approach is a layered one, combining multiple techniques to create a robust defense against fraud. By using automated upfront checks, verifying identities directly, and leveraging behind the scenes technical analysis, you can significantly improve the quality and reliability of your data.
This is especially true in growing research markets across Africa and other regions, where new digital methods are unlocking amazing insights. Platforms are rising to the challenge by integrating these safeguards directly into their workflow. For instance, platforms that operate on WhatsApp provide an inherent layer of phone number verification and can monitor response quality in real time. See why WhatsApp is ideal for market research in Africa.
By investing in proper verification, you protect your budget, your data, and the strategic decisions that depend on it.
Ready to run secure, high quality research with confidence? Request a WhatsApp research software demo to see how these verification best practices are built into a seamless WhatsApp experience.
Frequently Asked Questions
1. What is the most important step for how to verify participant identity in remote studies?
A multi layered approach is always best, but a great starting point is combining automated checks like CAPTCHAs and invitation only links with a simple direct check, such as a pre screen knowledge question or a digital footprint analysis.
2. Can you verify identity without asking for a government ID?
Absolutely. Methods like a digital footprint check, a live confirmation call, credential verification (like checking a LinkedIn profile), and pre screen knowledge checks can all help confirm a participant is real and qualified without requiring a sensitive document.
3. How much does participant verification add to the cost of a study?
Costs vary widely. Basic platform features (like duplicate prevention) are often included for free. Third party services like fraud risk scoring might cost a few cents per check. More intensive methods like live confirmation calls require staff time. The key is to balance the cost against the risk of collecting fraudulent data. For ballpark platform costs, see Yazi’s pricing.
4. Why is participant verification so important for research in emerging markets like Africa?
In markets where formal identity databases may be less comprehensive but mobile penetration (especially WhatsApp) is high, digital verification methods are crucial. Techniques like checking a person’s digital footprint via their phone number and leveraging trusted platforms help ensure data quality and representation where traditional methods might fall short.
5. How can AI help with verifying participant identity?
AI can automate many verification tasks. It can be used in video verification to match a live face to a photo ID, analyze digital footprints for signs of fraud, and power risk scoring algorithms that check hundreds of data points in milliseconds to identify suspicious participants.
6. What’s the best way to handle consent for identity checks?
Be transparent and upfront. Provide a clear, easy to understand privacy notice before any data is collected. Explain what data you are collecting, why you need it (to prevent fraud and ensure data quality), how it will be stored securely, and for how long. This builds trust and is required by data privacy laws like GDPR and POPIA.
%202.png)


.png)
